Pentesting
Website and Cloud
Security Check
Sometimes attacking is the best way to defend. Our penetration testing services simulate a cyberattack to check your website or cloud security and identify existing exploitable vulnerabilities.
Exact Pen Test scope
All vulnerabilities that will be tested are described in detail so you know exactly what you are paying for.
Easy to launch
Provide the domain to your website you want to have checked and thats it. No further information or special access rights from your side required.
Results in 7 days*
Receive the test results in up to 7 business days maximum.
*for SMALL PACKAGE offering
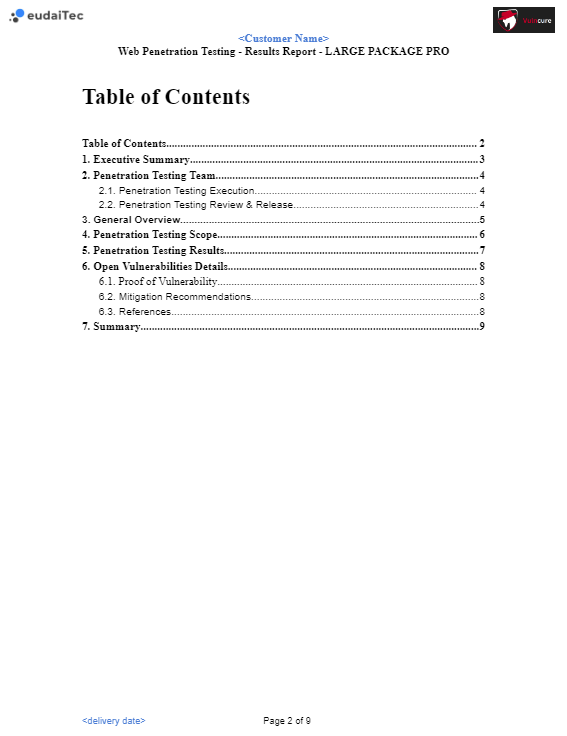
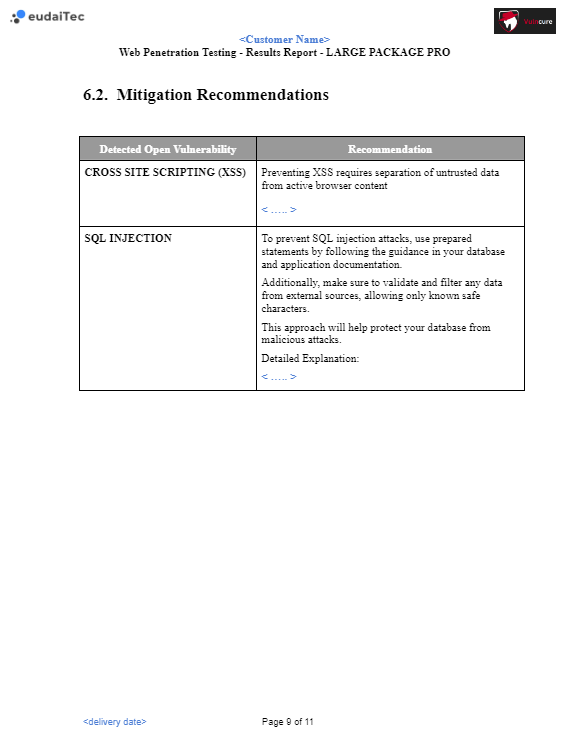
Mitigation Proposal*
You will be provided with a tailored proposal outlining strategies recommended to mitigate identified vulnerabilities
*delivered in PRO packages
Understanding our service and its benefits for you
Our ‘Website and Cloud Security Check’ goes beyond basic analysis to offer comprehensive penetration testing (pentesting). This essential service examines your site for vulnerabilities that hackers could exploit, simulating real-world attacks in a controlled environment. By identifying these weaknesses, our service not only enhances your website’s security but also mitigates risks and potentially prevents financial and reputational losses. Choose one of our Website Security Check packages to safeguard your digital presence effectively.
Choosing the right package
Understanding our packages: Our WebPen testing offerings come in three main types: SMALL, LARGE, API, and AWS CLOUD. Each is designed with different business sizes and needs in mind.
- SMALL Package: Best for startups and small businesses looking for foundational security assessments.
- LARGE Package: Ideal for businesses with Web Apps, E-Commerce Sites or Dynamic Apps requiring in-depth vulnerability analysis and extensive testing.
- API Package: Tailored for companies utilizing APIs extensively, needing specialized security assessments.
- AWS CLOUD Package: Perfect for businesses leveraging AWS cloud technology, offering comprehensive security assessments of cloud infrastructure.
Small
Package
899€
per domain
For informative Websites
with or without a simple contact form
Tested Vulnerabilities
Deliverable
Re-Test including Re-Test Report
Lead Time
7 working days
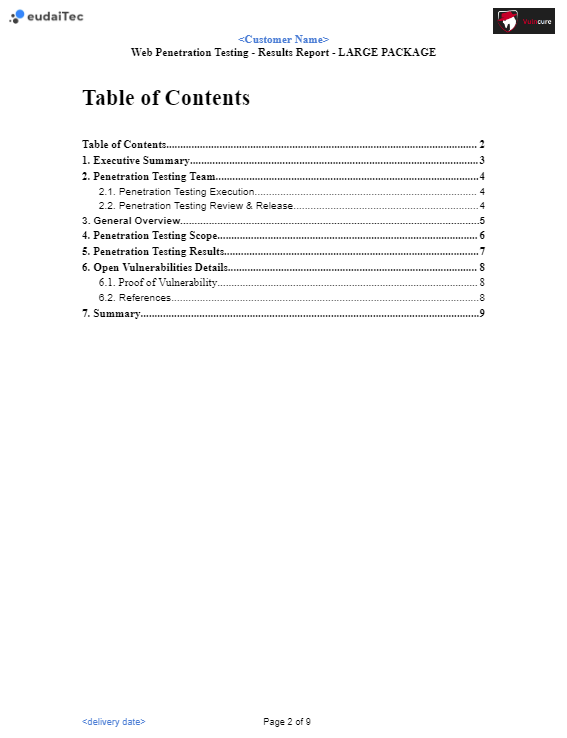
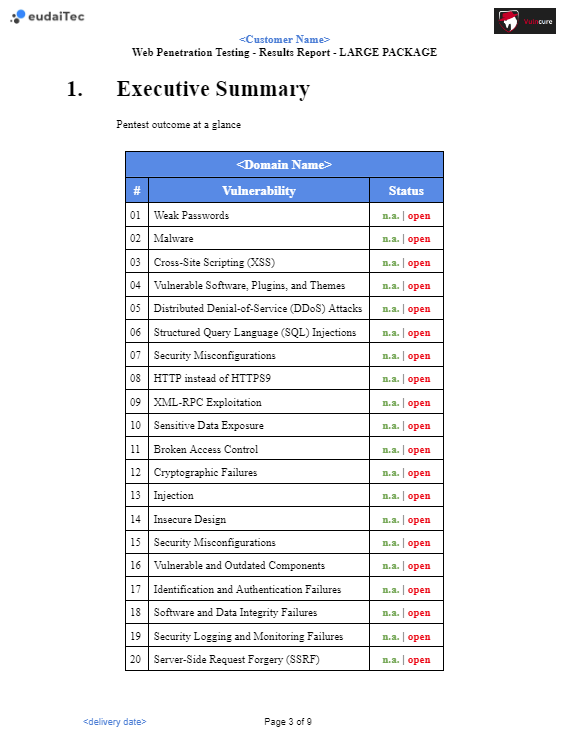
Large
Package
1499€
per domain
For Web Apps, E-Commerce Sites
or Dynamic Apps
Tested Vulnerabilities
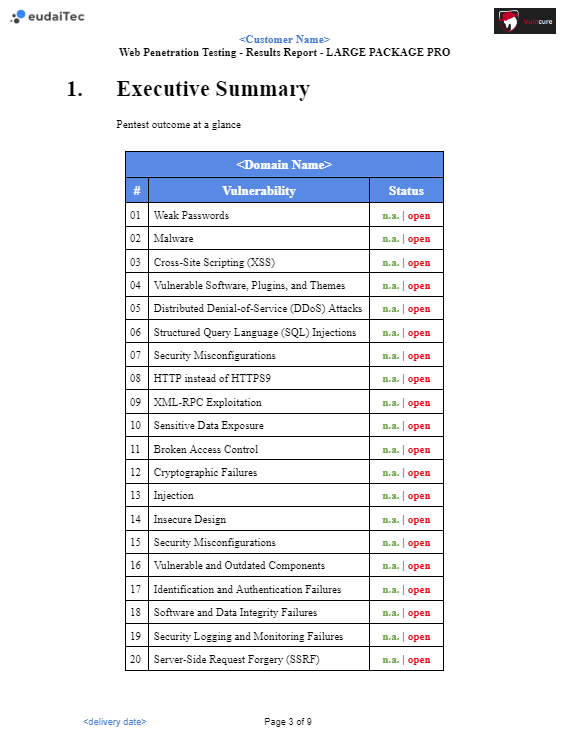
ALL VULNERABILITIES IN SMALL PACKAGE +
Broken Access Control
Cryptographic Failures
Injection
Insecure Design
Security Misconfigurations
Vulnerable and Outdated Components
Identification and Authentication Failures
Software and Data Integrity Failures
Security Logging and Monitoring Failures
Server-Side Request Forgery (SSRF)
Deliverable
Re-Test including Re-Test Report
Lead Time
14 working days
AWS CLOUD
Package
starting from
2499€
Tested Vulnerabilities
- Cloud, container or orchestration configuration
- Injection flaws
- Improper authentication & authorization
- CI/CD pipeline & software supply chain flaws
- Insecure secrets storage
- Over-permissive or insecure network policies
- Using components with known vulnerabilities
- Improper assets management
- Inadequate ‘compute’ resource quota limits
- Ineffective logging & monitoring
Deliverable
Re-Test including Re-Test Report
Lead Time
20 working days
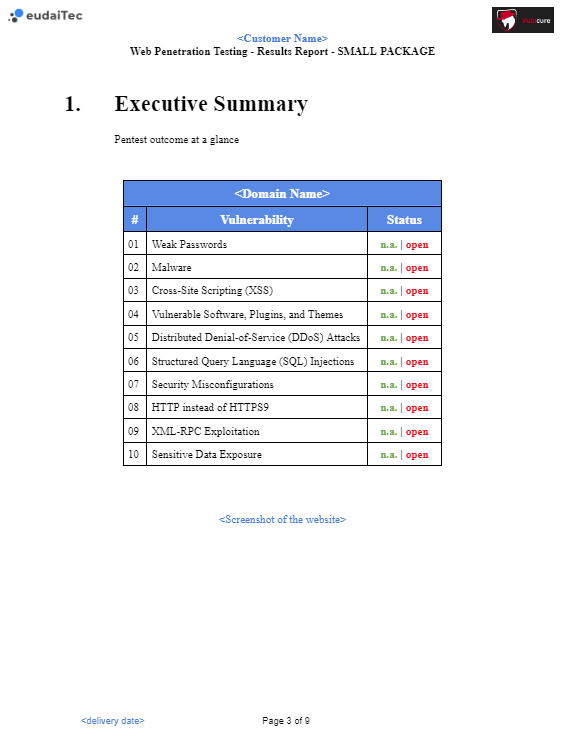
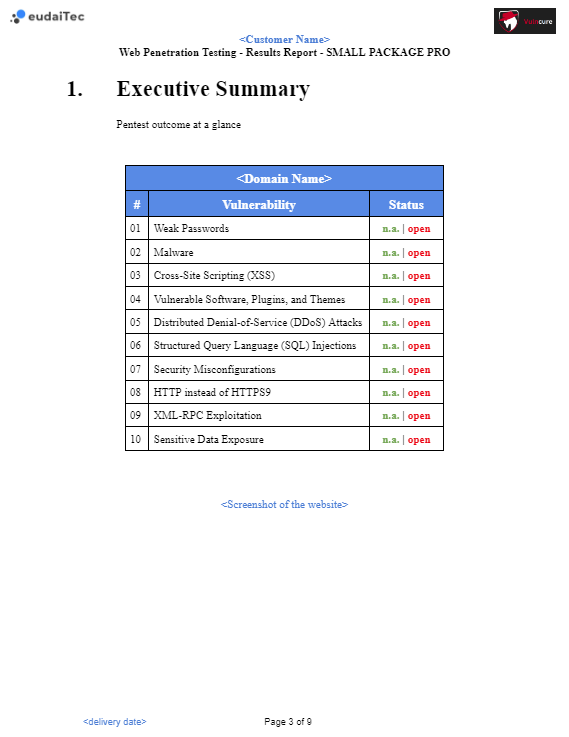
Weak Passwords
Description
Weak passwords refer to passwords that are easily guessable or susceptible to brute-force attacks due to their simplicity.
Possible negative impact
Unauthorized access to user accounts, data breaches, and compromised systems.
Malware
Description
Malware is malicious software designed to harm or exploit systems, including viruses, trojans, ransomware, and spyware.
Possible negative impact
Data loss, system disruption, unauthorized access, and compromised integrity.
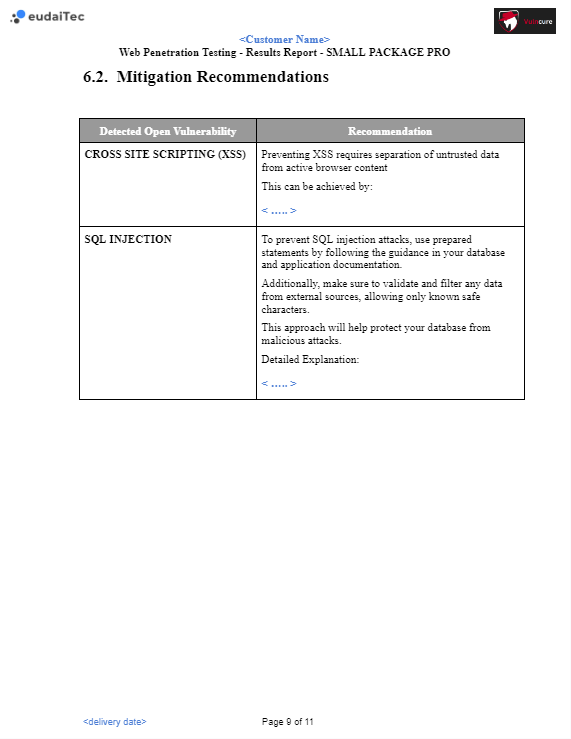
Cross-Site Scripting (XSS)
Description
XSS occurs when an attacker injects malicious scripts into web pages viewed by other users. This can lead to the theft of sensitive information.
Possible negative impact
Session hijacking, defacement of websites, stealing user data.
Vulnerable SOftware, Plugins and Themes
Description
The use of outdated or insecure software, plugins, or themes in web applications.
Possible negative impact
Exploitation of known vulnerabilities, unauthorized access, and compromise of the entire system.
Distributed Denial of Service (DDoS) Attacks
Description
DDoS attacks overwhelm a system by flooding it with traffic from multiple sources.
Possible negative impact
Service disruption, downtime, and potential data breaches.
SQL
Injection
Description
SQL injection is an attack technique where an attacker inserts malicious SQL code into user inputs, exploiting vulnerabilities in the application’s database layer.
Possible negative impact
Unauthorized access to sensitive data, data manipulation, and potential system compromise.
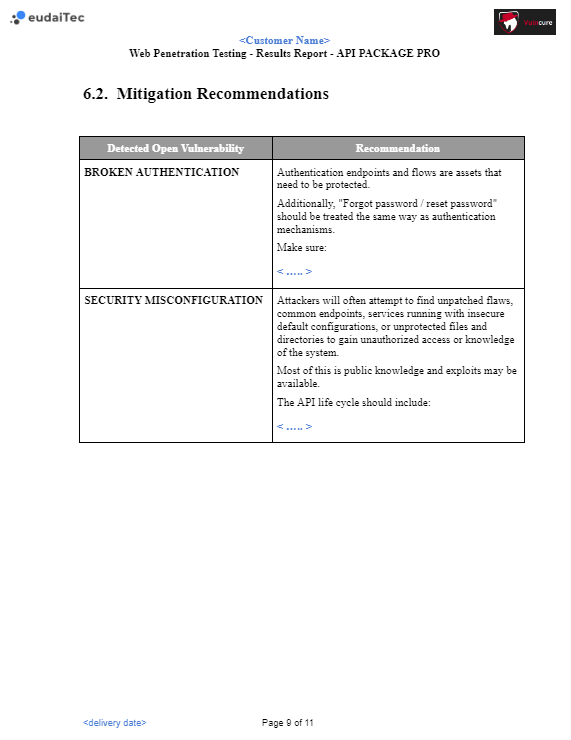
Security Misconfiguration
Description
Security misconfigurations arise from improperly configured settings, permissions
or access controls.
Possible negative impact
Unauthorized access, data exposure, and system vulnerabilities.
HTTP instead
of HTTPS9
Description
Using unencrypted HTTP instead of the secure HTTPS for transmitting data.
Possible negative impact
Data interception, man-in-the-middle attacks, and privacy breaches.
XML-RPC Exploitation
Description
XML-RPC exploitation involves abusing XML-RPC functionality to launch attacks on web applications.
Possible negative impact
Unauthorized access, data exposure, and potential compromise of the server.
Sensitive Data Exposure
Description
Involves the exposure of sensitive information, such as passwords or financial data, without adequate protection.
Possible negative impact
Unauthorized access to confidential information, leading to potential data breaches.
OWASP WEB
Top 10 2021
Description
OWASP WEB TOP 10 is a standard awareness document for web application security. It represents a broad consensus about the most critical security risks to web applications.
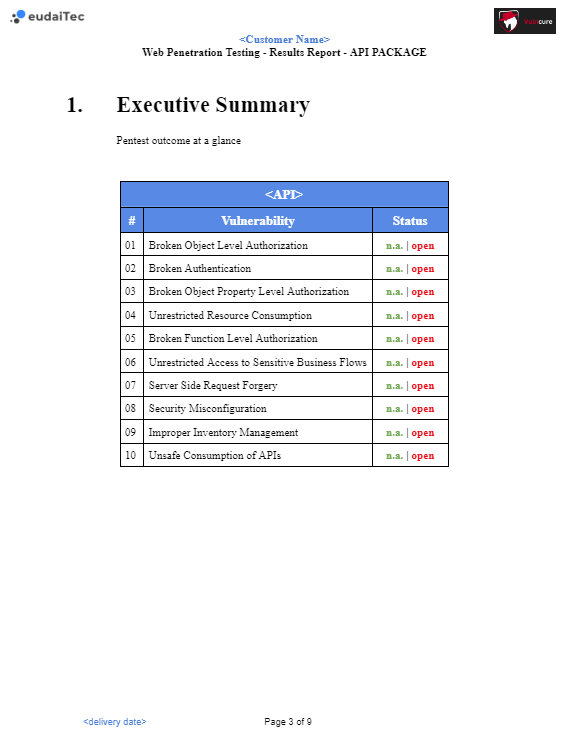
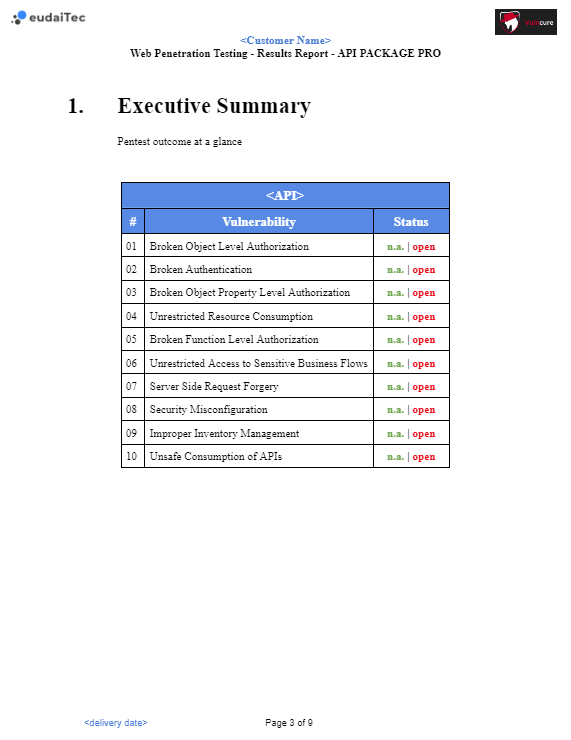
OWASP API
Top 10 2023
Description
API Security focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of Application Programming Interfaces (APIs).
A foundational element of innovation in today’s app-driven world is the API. By nature, APIs expose application logic and sensitive data such as Personally Identifiable Information (PII) and because of this have increasingly become a target for attackers. Without secure APIs, rapid innovation would be impossible.
Contact
eudaiTec GmbH
Siegfriedstr. 19
13156 Berlin